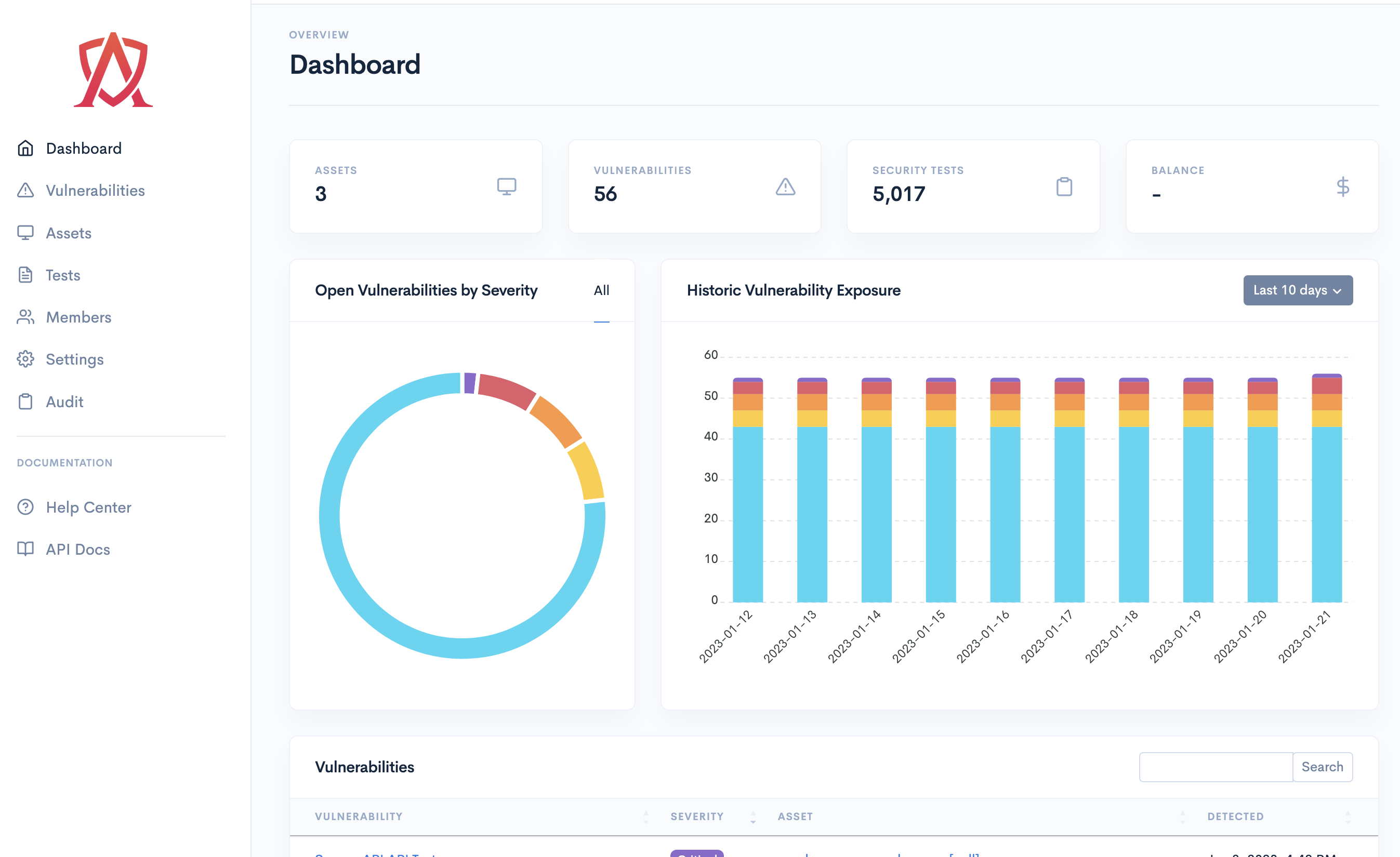
Continuously defend your organization's attack surface.
Proactively monitor all of your applications, servers, endpoints and cloud infrastructure by combining automation and expert-driven testing to continuously identify and remediate vulnerabilities.
Request a Demo Learn more